![]()
We are pleased to announce many new projects for computer science students at our new site. Do check them out and contribute to the collection. Cheers… 🙂
More Computer Projects
![]()
“Only force rules. Force is the first law”
– Adolf Hitler
For some unknown reasons I have always felt that all the efforts of leaders like Mahatama Gandhi, MLK, Nelson Mandela have gone in vain. Ugly incidences of violence in the name of race and color every now and then mock the achievements of these great leaders. The latest ones in Australia are just another addition to this list.
However the people of India are strong. They have faced and overthrown a white race before too. Its those so called white supermacist I am worried about. Will they be able to face the consequences of their wrongdoings. Also, what the special strength are they so proud about. It were these black hard working people whose toils and incessant hardwork in erstwhile British colonies generated the bounties which these white ones enjoy now. Even today the scenario remains the same.
Let me begin with the Indians themselves , who are so far the prime casualties in these atrocities. First of all Australia should be prepared of the immense monetary loss its going to face by losing the indian students in its universities. Also the bad name is surely going to spread to other countries also who will then detest from sending their kids to Australia fearing they might be next. Just to show how weak and hollow the so called white supermacy is, just put all the indian techies on hold for one day and see how all their infrastructure and stock market bite the dust.
However the most fearsome consequence which they may to face is a violent retaliation. They might be lucky that they started off with the Indians. Had they started with some of our hot blooded neigbors they might have already heard the loud noises. However every living being when pushed beyond the edge resort either to fight or flight. Its times like these when I have to hesitatingly support terrorism. What else the ordinary person can do in such situations? They are invited, given false promises of better future, made to pay in lakhs and then ultimately insulted and killed. Any similar act in any sane legislation system is sure to draw capital punishment. Then why Australia should go scot free? [The reason I blame whole country now is that because now even the police forces there have resorted to violence against innocent and unarmed indians. Politicians have turned in a blind eye.]
Perhaps what they now need are some Bhagat Singh and Subash Chandra Bose. What amuses me is that the race which shits it pants out even on a small bomb explosion is exihibiting its super-strength. Wait till the ball falls in your court. What has taken decades to die down in various forms like Taliban, LTTE etc. is going to reincarnate by foolish acts of yours. Then at the end don’t come out crying to world stage when your fancy buildings with sophisticated offices and educational institutes will be decimated to grounds, the places which you promised to these indians.
Hi visitor,
We have moved to our own site now. To visit us and view our blog please click the logo below…
 i.e. dheerajsuthar.com
i.e. dheerajsuthar.com
We regret for inconvenience.

The portrayal of hackers in the media has ranged from the high-tech super-spy, as
in Mission Impossible where Ethan Hunt repels from the ceiling to hack the CIA
computer system and steal the “NOC list,” to the lonely anti-social teen who is
simply looking for entertainment.
The reality, however, is that hackers are a very diverse bunch, a group
simultaneously blamed with causing billions of dollars in damages as well as
credited with the development of the World Wide Web and the founding of major tech
companies. In this article, we test the theory that truth is better than fiction
by introducing you to ten of the most famous hackers, both nefarious and heroic,
to let you decide for yourself.
Black Hat Crackers
The Internet abounds with hackers, known as crackers or “black hats,” who work to
exploit computer systems. They are the ones you’ve seen on the news being hauled
away for cybercrimes. Some of them do it for fun and curiosity, while others are
looking for personal gain. In this section we profile five of the most famous and
interesting “black hat” hackers.
1. Jonathan James: James gained notoriety when he became the first juvenile to be
sent to prison for hacking. He was sentenced at 16 years old. In an anonymous PBS
interview, he professes, “I was just looking around, playing around. What was fun
for me was a challenge to see what I could pull off.”
James’ major intrusions targeted high-profile organizations. He installed a
backdoor into a Defense Threat Reduction Agency server. The DTRA is an agency of
the Department of Defense charged with reducing the threat to the U.S. and its
allies from nuclear, biological, chemical, conventional and special weapons. The
backdoor he created enabled him to view sensitive e-mails and capture employee
usernames and passwords.
James also cracked into NASA computers, stealing software worth approximately $1.7
million. According to the Department of Justice, “The software supported the
International Space Station’s physical environment, including control of the
temperature and humidity within the living space.” NASA was forced to shut down
its computer systems, ultimately racking up a $41,000 cost. James explained that
he downloaded the code to supplement his studies on C programming, but contended,
“The code itself was crappy . . .certainly not worth $1.7 million like they
claimed.”
Given the extent of his intrusions, if James, also known as “c0mrade,” had been an
adult he likely would have served at least ten years. Instead, he was banned from
recreational computer use and was slated to serve a six-month sentence under house
arrest with probation. However, he served six months in prison for violation of
parole. Today, James asserts that he’s learned his lesson and might start a
computer security company.
2. Adrian Lamo: Lamo’s claim to fame is his break-ins at major organizations like
The New York Times and Microsoft. Dubbed the “homeless hacker,” he used Internet
connections at Kinko’s, coffee shops and libraries to do his intrusions. In a
profile article, “He Hacks by Day, Squats by Night,” Lamo reflects, “I have a
laptop in Pittsburgh, a change of clothes in D.C. It kind of redefines the term
multi-jurisdictional.”
Lamo’s intrusions consisted mainly of penetration testing, in which he found flaws
in security, exploited them and then informed companies of their shortcomings. His
hits include Yahoo!, Bank of America, Citigroup and Cingular. When white hat
hackers are hired by companies to do penetration testing, it’s legal. What Lamo
did is not.
When he broke into The New York Times’ intranet, things got serious. He added
himself to a list of experts and viewed personal information on contributors,
including Social Security numbers. Lamo also hacked into The Times’ LexisNexis
account to research high-profile subject matter.
For his intrusion at The New York Times, Lamo was ordered to pay approximately
$65,000 in restitution. He was also sentenced to six months of home confinement
and two years of probation, which expired January 16, 2007. Lamo is currently
working as an award-winning journalist and public speaker.
3. Kevin Mitnick: A self-proclaimed “hacker poster boy,” Mitnick went through a
highly publicized pursuit by authorities. His mischief was hyped by the media but
his actual offenses may be less notable than his notoriety suggests. The
Department of Justice describes him as “the most wanted computer criminal in
United States history.” His exploits were detailed in two movies: Freedom Downtime
and Takedown.
Mitnick had a bit of hacking experience before committing the offenses that made
him famous. He started out exploiting the Los Angeles bus punch card system to get
free rides. Then, like Apple co-founder Steve Wozniak, dabbled in phone phreaking.
Although there were numerous offenses, Mitnick was ultimately convicted for
breaking into the Digital Equipment Corporation’s computer network and stealing
software.
Mitnick’s mischief got serious when he went on a two and a half year “coast-to-
coast hacking spree.” The CNN article, “Legendary computer hacker released from
prison,” explains that “he hacked into computers, stole corporate secrets,
scrambled phone networks and broke into the national defense warning system.” He
then hacked into computer expert and fellow hacker Tsutomu Shimomura’s home
computer, which led to his undoing.
Today, Mitnick has been able to move past his role as a black hat hacker and
become a productive member of society. He served five years, about 8 months of it
in solitary confinement, and is now a computer security consultant, author and
speaker.
4. Kevin Poulsen: Also known as Dark Dante, Poulsen gained recognition for his
hack of LA radio’s KIIS-FM phone lines, which earned him a brand new Porsche,
among other items. Law enforcement dubbed him “the Hannibal Lecter of computer
crime.”
Authorities began to pursue Poulsen after he hacked into a federal investigation
database. During this pursuit, he further drew the ire of the FBI by hacking into
federal computers for wiretap information.
His hacking specialty, however, revolved around telephones. Poulsen’s most famous
hack, KIIS-FM, was accomplished by taking over all of the station’s phone lines.
In a related feat, Poulsen also “reactivated old Yellow Page escort telephone
numbers for an acquaintance who then ran a virtual escort agency.” Later, when his
photo came up on the show Unsolved Mysteries, 1-800 phone lines for the program
crashed. Ultimately, Poulsen was captured in a supermarket and served a sentence
of five years.
Since serving time, Poulsen has worked as a journalist. He is now a senior editor
for Wired News. His most prominent article details his work on identifying 744 sex
offenders with MySpace profiles.
5. Robert Tappan Morris: Morris, son of former National Security Agency scientist
Robert Morris, is known as the creator of the Morris Worm, the first computer worm
to be unleashed on the Internet. As a result of this crime, he was the first
person prosecuted under the 1986 Computer Fraud and Abuse Act.
Morris wrote the code for the worm while he was a student at Cornell. He asserts
that he intended to use it to see how large the Internet was. The worm, however,
replicated itself excessively, slowing computers down so that they were no longer
usable. It is not possible to know exactly how many computers were affected, but
experts estimate an impact of 6,000 machines. He was sentenced to three years’
probation, 400 hours of community service and a fined $10,500.
Morris is currently working as a tenured professor at the MIT Computer Science and
Artificial Intelligence Laboratory. He principally researches computer network
architectures including distributed hash tables such as Chord and wireless mesh
networks such as Roofnet.
White Hat Hackers
Hackers that use their skills for good are classified as “white hat.” These white
hats often work as certified “Ethical Hackers,” hired by companies to test the
integrity of their systems. Others, operate without company permission by bending
but not breaking laws and in the process have created some really cool stuff. In
this section we profile five white hat hackers and the technologies they have
developed.
1. Stephen Wozniak: “Woz” is famous for being the “other Steve” of Apple. Wozniak,
along with current Apple CEO Steve Jobs, co-founded Apple Computer. He has been
awarded with the National Medal of Technology as well as honorary doctorates from
Kettering University and Nova Southeastern University. Additionally, Woz was
inducted into the National Inventors Hall of Fame in September 2000.
Woz got his start in hacking making blue boxes, devices that bypass telephone-
switching mechanisms to make free long-distance calls. After reading an article
about phone phreaking in Esquire, Wozniak called up his buddy Jobs. The pair did
research on frequencies, then built and sold blue boxes to their classmates in
college. Wozniak even used a blue box to call the Pope while pretending to be
Henry Kissinger.
Wozniak dropped out of college and came up with the computer that eventually made
him famous. Jobs had the bright idea to sell the computer as a fully assembled PC
board. The Steves sold Wozniak’s cherished scientific calculator and Jobs’ VW van
for capital and got to work assembling prototypes in Jobs’ garage. Wozniak
designed the hardware and most of the software. In the Letters section of Woz.org,
he recalls doing “what Ed Roberts and Bill Gates and Paul Allen did and tons more,
with no help.” Wozniak and Jobs sold the first 100 of the Apple I to a local
dealer for $666.66 each.
Woz no longer works full time for Apple, focusing primarily on philanthropy
instead. Most notable is his function as fairy godfather to the Los Gatos School
District. “Wozniak ‘adopted’ the Los Gatos School District, providing students and
teachers with hands-on teaching and donations of state-of-the-art technology
equipment.”
2. Tim Berners-Lee: Berners-Lee is famed as the inventor of the World Wide Web,
the system that we use to access sites, documents and files on the Internet. He
has received numerous recognitions, most notably the Millennium Technology Prize.
While a student at Oxford University, Berners-Lee was caught hacking access with a
friend and subsequently banned from University computers. w3.org reports, “Whilst
[at Oxford], he built his first computer with a soldering iron, TTL gates, an
M6800 processor and an old television.” Technological innovation seems to have run
in his genes, as Berners-Lee’s parents were mathematicians who worked on the
Manchester Mark1, one of the earliest electronic computers.
While working with CERN, a European nuclear research organization, Berners-Lee
created a hypertext prototype system that helped researchers share and update
information easily. He later realized that hypertext could be joined with the
Internet. Berners-Lee recounts how he put them together: “I just had to take the
hypertext idea and connect it to the TCP and DNS ideas and – ta-da! – the World
Wide Web.”
Since his creation of the World Wide Web, Berners-Lee founded the World Wide Web
Consortium at MIT. The W3C describes itself as “an international consortium where
Member organizations, a full-time staff and the public work together to develop
Web standards.” Berners-Lee’s World Wide Web idea, as well as standards from the
W3C, is distributed freely with no patent or royalties due.
3. Linus Torvalds: Torvalds fathered Linux, the very popular Unix-based operating
system. He calls himself “an engineer,” and has said that his aspirations are
simple, “I just want to have fun making the best damn operating system I can.”
Torvalds got his start in computers with a Commodore VIC-20, an 8-bit home
computer. He then moved on to a Sinclair QL. Wikipedia reports that he modified
the Sinclair “extensively, especially its operating system.” Specifically,
Torvalds hacks included “an assembler and a text editor…as well as a few games.”
Torvalds created the Linux kernel in 1991, using the Minix operating system as
inspiration. He started with a task switcher in Intel 80386 assembly and a
terminal driver. After that, he put out a call for others to contribute code,
which they did. Currently, only about 2 percent of the current Linux kernel is
written by Torvalds himself. The success of this public invitation to contribute
code for Linux is touted as one of the most prominent examples of free/open source
software.
Currently, Torvalds serves as the Linux ringleader, coordinating the code that
volunteer programmers contribute to the kernel. He has had an asteroid named after
him and received honorary doctorates from Stockholm University and University of
Helsinki. He was also featured in Time Magazine’s “60 Years of Heroes.”
4. Richard Stallman: Stallman’s fame derives from the GNU Project, which he
founded to develop a free operating system. For this, he’s known as the father of
free software. His “Serious Bio” asserts, “Non-free software keeps users divided
and helpless, forbidden to share it and unable to change it. A free operating
system is essential for people to be able to use computers in freedom.”
Stallman, who prefers to be called rms, got his start hacking at MIT. He worked as
a “staff hacker” on the Emacs project and others. He was a critic of restricted
computer access in the lab. When a password system was installed, Stallman broke
it down, resetting passwords to null strings, then sent users messages informing
them of the removal of the password system.
Stallman’s crusade for free software started with a printer. At the MIT lab, he
and other hackers were allowed to modify code on printers so that they sent
convenient alert messages. However, a new printer came along – one that they were
not allowed to modify. It was located away from the lab and the absence of the
alerts presented an inconvenience. It was at this point that he was “convinced…of
the ethical need to require free software.”
With this inspiration, he began work on GNU. Stallman wrote an essay, “The GNU
Project,” in which he recalls choosing to work on an operating system because it’s
a foundation, “the crucial software to use a computer.” At this time, the
GNU/Linux version of the operating system uses the Linux kernel started by
Torvalds. GNU is distributed under “copyleft,” a method that employs copyright law
to allow users to use, modify, copy and distribute the software.
Stallman’s life continues to revolve around the promotion of free software. He
works against movements like Digital Rights Management (or as he prefers, Digital
Restrictions Management) through organizations like Free Software Foundation and
League for Programming Freedom. He has received extensive recognition for his
work, including awards, fellowships and four honorary doctorates.
5. Tsutomu Shimomura: Shimomura reached fame in an unfortunate manner: he was
hacked by Kevin Mitnick. Following this personal attack, he made it his cause to
help the FBI capture him.
Shimomura’s work to catch Mitnick is commendable, but he is not without his own
dark side. Author Bruce Sterling recalls: “He pulls out this AT&T cellphone, pulls
it out of the shrinkwrap, finger-hacks it, and starts monitoring phone calls going
up and down Capitol Hill while an FBI agent is standing at his shoulder, listening
to him.”
Shimomura out-hacked Mitnick to bring him down. Shortly after finding out about
the intrusion, he rallied a team and got to work finding Mitnick. Using Mitnick’s
cell phone, they tracked him near Raleigh-Durham International Airport. The
article, “SDSC Computer Experts Help FBI Capture Computer Terrorist” recounts how
Shimomura pinpointed Mitnick’s location. Armed with a technician from the phone
company, Shimomura “used a cellular frequency direction-finding antenna hooked up
to a laptop to narrow the search to an apartment complex.” Mitnick was arrested
shortly thereafter. Following the pursuit, Shimomura wrote a book about the
incident with journalist John Markoff, which was later turned into a movie.
Hi visitor,
More here
 i.e. dheerajsuthar.com
i.e. dheerajsuthar.com
‘Zeitgeist’ is basically a german expression meaning ‘the spirit of the times or the ages’. As a movement its the activist arm of the ‘Venus Project’ envisaged by well known industrial designer Jacque Fresco. It aims at creating a new social structure free from the tyranny of religion, government and economy. It relies on technology as the major aid in creating such a self dependent resourceful civilization.

A critical review
To make our review fair we will discuss both sides of coin. First of all we can talk of the benefits and the positive aspect of Zeitgeist movement.
Advantages:
- The movement clearly attacks on some of the major source of miseries of human beings viz. politics, religion, economic domination and media. These so called pillars of modern society have been corrupted by some clever and dominating people for their own benefits. The proofs given in the documentaries really appear startling and present the whole dirty nexus rather than parts of it.
- Goes beyond conspiracy theories- Numerous 9/11 conspiracies have been made since the tragic incidence. Rather than exposing the whole reality they have just scared the people. However this documentary goes beyond that revealing the whole vicious circle including the political heads of America.It has also digged the historical developments so that all pieces fits correctly in the jigsaw puzzle.Also the viewers become more enligthened about the real culprits behind the Depression.
- Finally a solution- It just doesn’t leaves the viewers in blank rather suggest them a way to overcome this rut.’Technology’ is correctly suggested as the Samaritan(which it has been since the discovery of wheel). Also the direct confrontation to the government via non payment of taxes reminds one of peaceful yet brilliantly successful non-cooperation movements by Mahatma Gandhi.
- Mass movement- Despite being rebellious in nature this movement is gaining popularity even beyond the country of its origin.In 2008 there were 1800 events held in 70 nations around the world. Now that’s something enthralling. If any such freedom movement seeks to be successful then it will have to take whole world along with it especially developing countries which are still in the stage of transformation.
Few shortcomings
As with every movement this one suffers from some lacunae too.
- First of all the whole political scenario it basis itself upon doesn’t applies to every country in the world. For e.g. in India ‘Non-payment of taxes is really punishable offence’. Also the topmost economic authority, the Reserve Bank of India is totally government/public institute. Similarly, in many middle eastern countries Islam is protected by government and is followed by their residents with the faith beyond any doubts. Any movement denying religion will rather draw criticism than praise there.
- One man theory- This is one of the alarming trait which has brought doom to nearly every great movements in the past which were totally ran as one-man show. Its not that there are any doubts on the abilities of Jacque Fresco, but it again create a sort of dependency and blind faith on single person. Worse still, any unacceptable personal act of this person or his close ones can bring the suspicion to the whole ideology of movement itself (remember Rajneeshpuram).
- Over-dependence on technology- Although techonology is useful for recreation of a better society but sole dependence on them is not advisable. Who can guarntee their use or misuse. Some sort of control measures must be required to prevent crimes and other disturbing activities which human mind can think of. Else with extreme technology at hand the results may be devastating beyond calculation. One of the measure might be constant brain mapping of every person on earth. Its a task which is both difficult and funny because if implemented it will create another form of domination; domination against which we created the whole movement (remember RFID).
However it will be very inappropriate to be sarcastic as this movement is in its stage of evolution. In due course of time it may become more refined and may finally be adopted by the world. Atleast a step in right direction is far better than doing nothig about the deteroiting conditions. Also who knows what started from something as small as a documentary may end up bringing a great change to the world, like the way a small project started by a Finnish student developed in to something as huge and beautiful as Linux. 😉
Resources

More here…
 i.e. dheerajsuthar.com
i.e. dheerajsuthar.com

At last our most beloved blogger is back from his ‘voyage of solitude’. Apparently he appears enlightened now and talk the language of the wise. Some strange but beneficiary things he has done now is:
- Made ‘Ubuntu’ the default operating system for the whole group (Although bit frustrating at first the the transformation is now complete… it has totally replaced the Windows from our machines and head too…)
- Talk of peaceful solutions to all disputes and preaches to practice ‘silence’ (or what he calls mauna and dhyana). Its unbelievable but true… However his silent ways are appearing to be lot more effective than his previous roars of violence.
- He is planning to divide the blog in to many subunits as due to its size and varied content its now appearing to cumbersome to maintain.
- More user oriented things like free softwares, projects for students will be included.
- He has strongly opposed the post about ‘Zeitgeist’ and has praised the movement as another sign of enlightenment. On the contrary, he has instructed us to spread the word.
So, from now on Sher Khan will be the main publisher. Let the wise tree speak…
Laakhan
For further contact:
Sher Khan
(mail:
sherkhan_20052005@yahoo.com
sherkhan666@in.com (GPG encryption supported))

Our Public Key:
—–BEGIN PGP PUBLIC KEY BLOCK—–
Version: GnuPG v1.4.9 (GNU/Linux)
mQGiBEoHKikRBACwqUrXeM7ar/W5QKzr8h949snVrIFS52dRrJwXxRrnYOw0Mwn+
ozpnmA5ITC4mPTdhoGINEnlDtvNZhp48pDEqB42E4bTjo+B7G7rr5UMaawSaltD/
rO+cBgZQGjmRfu7Jc4k5PR/RYjfs0nDu8jjANXkeh/qUYVTR5zFbAqn8rwCg1Qv1
A0I9p4tQYTzLbQUeLRe2QzcD/jLrAqh7gyWQrx7E3FEjI708yiH+RP712R6i33wk
w2peEAcv5qt+94rREJPHhb3bDCHPMSEC4YzKltPXKgpzHMk3iO/BLPn+DMJ/p+f8
ClTM1hwg8F/DmeGyUNVYGrNvlRM+fQSQ1gl+tPFZX+Xxoj0XYrrtN78WemtjzcPr
wwfJA/sEJbp87nEdp7Znd4GZcVvhRj6/E5EmWdhQVd9bszkOUzQpLhMPqqZ9DUnb
kBjqtGegHb04hnbS5WWdawD5nNy1l25/JRjsALpZAJCJIoJora+9uEzmOnQFY/Pm
G986b2WYublRJ+zWDdvhyofU/JViO629H9YjqUHtdxqPlMkxHLQvZGhlZXJhaiBz
dXRoYXIgKGZvciBmaWxlcykgPHNoZXJraGFuNjY2QGluLmNvbT6IYAQTEQIAIAUC
SgcqKQIbIwYLCQgHAwIEFQIIAwQWAgMBAh4BAheAAAoJEAiNW1SZWsbaIDoAoL5n
oiTYLBJrLS6HUM75m9Izc7o7AKCpT6y0s6DEBq9BCtvlXhu7kvadeLkCDQRKByop
EAgAlQ9XGlIn+xKJQO0BviUk6o6+gYMPqvCnB33SJxHz92DPRcHcNpuVXEZlN5py
WklEV/gIdijG508hvzmlkBrJI25M8KD4nMxupqRdTiXXJS5qkDdFfM8nFyGka5Se
Zxq4uni0PVzj+7hfGTLcv2jYs6KxHvDTh1Jh3y9CIRauUBEHfU19GVpn8RUbeTvh
Z+SPQf0z4ktyLHcXAkRK/H9QGetiRn4w0AiEfYvrZCx5VPkthm5Fb7mt/It430b1
IsHgUozGTJdARcJzRN2J6XD08UCaO4Wl7QVfAJy+x59ywtvaErXKgFxezcxHMFgr
/O3XycA5YOLQT1bmiaaStirh0wADBQf/YkKMjk0hEODTbOgokN7rHwBgyPMDadLz
m3h7gMhGddLNico2I3uoEiseQ/wFLIs0KmqIvaY5JLiicLjLmfqjsNU9VVAt7ePD
5Yncom0xy/+1zjyvPE/ilTPMTkWq4WvZoIk3gyryshRg2R1b8uHZ/p4Xc0xSFWR4
Sfa1TIs59E4jy5JoKGEyvc+CNi8xPU5X4Sl3JRdf23zRpR22RteccMZZT9Z7pW3q
JCGsXh/kyQbkYFvJAjoPLQ9Kx/qNeISaB1Dqsu9KHNypI54rTsl+T4exTfSCWT/Z
xEDBSe/ATdgiCghWSRMccIQKk5ivd2XGBsRhjxuwOxUzPW5DzA/4pohJBBgRAgAJ
BQJKByopAhsMAAoJEAiNW1SZWsbaDUgAoNG5mJ2lWwR+cALTA169r2K7ErB8AJ47
Yb2zBnSCJCAvdcLR8+KwGjngBg==
=RxoY
—–END PGP PUBLIC KEY BLOCK—–
We support:
![]()
 Stumble It!
Stumble It!

More here…
 i.e. dheerajsuthar.com
i.e. dheerajsuthar.com
1. Ali Baba and the forty thieves are now Ali Baba and the thirty thieves. Ten were laid off.
2. Batman and Robin are now Batman and Pedro. Batman fired Robin and hired Pedro because Pedro was willing to work twice the hours at the same rate.
3. Iron man now “air-pooling” with Superman to save fuel costs.
4. Now for some good news, Women finally marrying for love, and not money!
5. Q:) With the current market turmoil, what’s the easiest way to make a small fortune?
A:) Start off with a large one.
6. The credit crunch is getting bad isn’t it? I mean, I let my brother borrow $50 a couple of weeks back, it turns out I’m now America’s third biggest lender.
7. Q:) Why has Dubai real estate agents stopped looking out of the window in the morning?
A:) Because otherwise they’d have nothing to do in the afternoon.
8. Q:) What’s the difference between an American and a Zimbabwean?
A:) In a few weeks, nothing.
9. Dow Jones is re-branded as “Down Jones”.
More here…
 i.e. dheerajsuthar.com
i.e. dheerajsuthar.com
Here is the link of projects of my and my friends made during our graduation…
Click here.
More on computers and OSS… Click here.
More soon…
More here…
 i.e. dheerajsuthar.com
i.e. dheerajsuthar.com
There have been moments in the human history when all its (human) hideous ugliness raises its head leaving a deep scar on our so called above-animal image. We may try to ignore it in name of ignorance but an electronic eye catches them…
 1957. The first day of Dorothy Counts at the Harry Harding High School in the United States. Counts was one of the first black students admitted in the school, and she was no longer able to stand the harassments after 4 days.
1957. The first day of Dorothy Counts at the Harry Harding High School in the United States. Counts was one of the first black students admitted in the school, and she was no longer able to stand the harassments after 4 days.
 January 12, 1960. A second before the Japanese Socialist Party leader Asanuma was murdered by an opponent student.
January 12, 1960. A second before the Japanese Socialist Party leader Asanuma was murdered by an opponent student.
-
 1963. Thich Quang Duc, the Buddhist priest in Southern Vietnam , burns himself to death protesting the government’s torture policy against priests. Thich Quang Dug never made a sound or moved while he was burning.
1963. Thich Quang Duc, the Buddhist priest in Southern Vietnam , burns himself to death protesting the government’s torture policy against priests. Thich Quang Dug never made a sound or moved while he was burning.
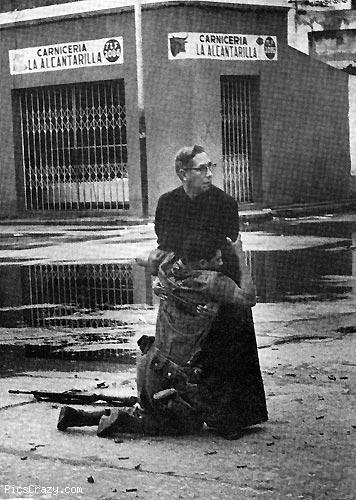 1962. A soldier shot by a sniper hangs onto a priest in his last moments.
1962. A soldier shot by a sniper hangs onto a priest in his last moments.
 1965. A mom and her children try to cross the river in South Vietnam in an attempt to run away from the American bombs.
1965. A mom and her children try to cross the river in South Vietnam in an attempt to run away from the American bombs.
 1966. U.S. troops in South Vietnam are dragging a dead Viet Kong soldier.
1966. U.S. troops in South Vietnam are dragging a dead Viet Kong soldier.
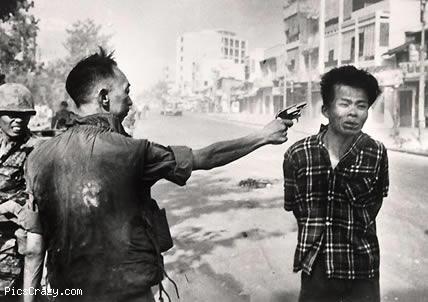 February 1, 1968. South Vietnam police chief Nguyen Ngoc Loan shots a young man, whom he suspects to be a Viet Kong soldier.
February 1, 1968. South Vietnam police chief Nguyen Ngoc Loan shots a young man, whom he suspects to be a Viet Kong soldier.
 1972. After South Vietnam planes accidentally drop a bomb on a town
1972. After South Vietnam planes accidentally drop a bomb on a town
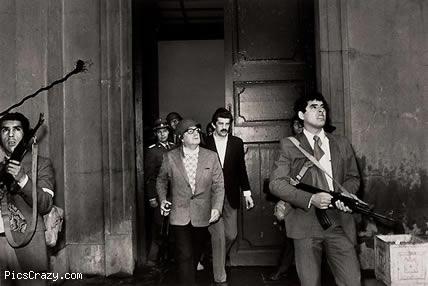 1973. A few seconds before Chile’s elected president Salvador Allende is dead during the coup.
1973. A few seconds before Chile’s elected president Salvador Allende is dead during the coup.
 1975. A woman and a girl falling down after the fire escape collapses
1975. A woman and a girl falling down after the fire escape collapses
 1980. A kid in Uganda about to die of hunger, and a missionary.
1980. A kid in Uganda about to die of hunger, and a missionary.
 February 23, 1981. Colonel Molina ve military police seizes the Parliament building in Spain. The photographer did not expect the scene, and hid the films in his shoe.
February 23, 1981. Colonel Molina ve military police seizes the Parliament building in Spain. The photographer did not expect the scene, and hid the films in his shoe.
 1987. A mother in South Korea apologizes and asks for forgiveness for his son who was arrested after attending a protest. He was protesting the alleged manipulations in the general elections.
1987. A mother in South Korea apologizes and asks for forgiveness for his son who was arrested after attending a protest. He was protesting the alleged manipulations in the general elections.
 1989. A young man in China stands before the tanks during protests for democratic reforms.
1989. A young man in China stands before the tanks during protests for democratic reforms.
 1992. A mother in Somalia holds the body of her child who died of hunger.
1992. A mother in Somalia holds the body of her child who died of hunger.
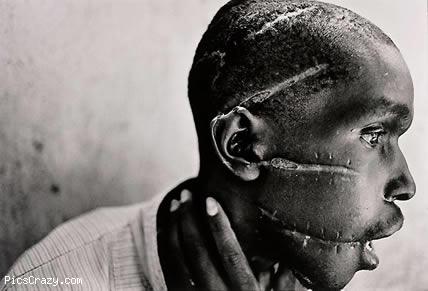 1994. A man who was tortured by the soldiers since he was suspected to have spoken with the Tutsi rebels.
1994. A man who was tortured by the soldiers since he was suspected to have spoken with the Tutsi rebels.

- 1996. Kids who are shocked by the civil war in Angola.

- 2001. An Afghani refugee kid’s body is being prepared for the funeral in Pakistan
 2002. Soldiers and villagers in Iran are digging graves for the victims of the earthquake. A kid holds his father’s pants before he is buried.
2002. Soldiers and villagers in Iran are digging graves for the victims of the earthquake. A kid holds his father’s pants before he is buried.
 2003. An Iraqi prisoner of war tries to calm down his child.
2003. An Iraqi prisoner of war tries to calm down his child.
More here…
 i.e. dheerajsuthar.com
i.e. dheerajsuthar.com